As of March 2026, CI-ISAC has raised and sustained the Cyber Threat Level at Elevated. The decision reflects a convergence of conditions that together represent a materially different risk environment for Australia’s critical infrastructure; not a single event, but several, and a number of them are distinctly Australian in character.
The sectors keeping this country running are operating in that environment right now. For operators, this elevation raises a question that goes beyond the designation itself: what does an elevated threat level actually mean in practice, and what does it demand of the organisations responsible for keeping essential services running?
What is an ‘Elevated’ Threat Level?
CI-ISAC’s Cyber Threat Level (CTL) system exists to give critical infrastructure operators a shared, real-time read on the national threat environment. Elevated is the second of four threat levels in CI-ISAC Australia’s Cyber Threat Level system, indicating that the threat landscape has shifted materially from business as usual.
An Elevated threat level indicates that significant, material cyber incidents are already causing operational impact across one or more sectors, or that additional security measures are being applied or recommended to operators.
It is not a worst-case scenario, but it is a signal that the organisations responsible for keeping essential services running should be operating with heightened awareness, not just routine vigilance.

Why the Threat Level Is Elevated
The current elevation is not a response to a single incident; it reflects a threat environment where multiple pressure points have converged simultaneously, each reinforcing the others.
One of the first pressure points was the Stryker cyberattack in March 2026, which was a coordinated attack on a US medical device manufacturer. During the incident, threat actors reportedly targeted the organisation’s Microsoft environment, executing remote wipes on Windows devices configured to connect to the company’s technology systems, which in turn caused a global outage. The incident did not stay within US borders; instead, the outage trickled down through supply chains and into Australia’s health operating environments within days.
In addition to this attack, Australia’s geopolitical position has also shifted in ways that open the door for direct cyber implications. A series of recent political decisions, including the deployment of RAAF assets to the Middle East and the granting of humanitarian visas to members of the Iranian women’s football team, have raised Australia’s profile within an active international conflict. That visibility has been noted, and active threat campaigns targeting Australian operators have since been observed and confirmed.
Together, these pressure points are creating a threat environment that demands more than routine vigilance from the organisations responsible for keeping essential services running. If you operate in Australia, and would like more details on the above factors, contact us here for the Detailed Threat Advisory.
What An Elevated Threat Level Means for Australian Critical Infrastructure Operators
For senior leaders responsible for Australia’s critical infrastructure sector, an Elevated threat level is not an instruction to act on every signal. Instead, it is a prompt to ask harder questions about whether your organisation has the visibility to distinguish the signals that matter from the noise.
The speed at which threats are materialising has changed the nature of the problem. What once gave security teams weeks or months to respond now gives them hours, and the organisations that are best prepared are the ones with the clearest picture of what is happening in their specific environment, and in the sectors around them.
The Stryker attack illustrated this directly; Australian operators did not need to be directly targeted to feel its consequences. The disruption arrived through a supply chain dependency, without warning, in a sector already under pressure. An organisation with visibility only within its own walls would have had little opportunity to anticipate it.
For boards already asking hard questions about operational continuity and cyber risk governance, the practical implication is straightforward: the organisations best positioned to navigate an elevated threat environment are those with access to intelligence that has been validated across sectors, assessed against Australian conditions, and delivered at the speed the environment demands.
The Intelligence Advantage That Changes the Equation
An Elevated threat level is, ultimately, a question directed at every organisation responsible for keeping essential services running: are you seeing enough, quickly enough, to stay ahead of what is coming?
The events of the past weeks have demonstrated that the answer to that question cannot come from within a single organisation’s walls. The threats shaping Australia’s current environment are cross-sector, fast-moving, and distinctly local in their implications. The intelligence needed to navigate them has to be too.
No single organisation has full visibility of the threat landscape, and fragmented intelligence limits the ability to respond at the speed the environment now demands. As the threat landscape becomes more complex and the pressure points multiply, the resilience of Australia’s essential services depends on trusted, cross-sector collaboration that enables intelligence to be shared, validated, and acted on collectively.
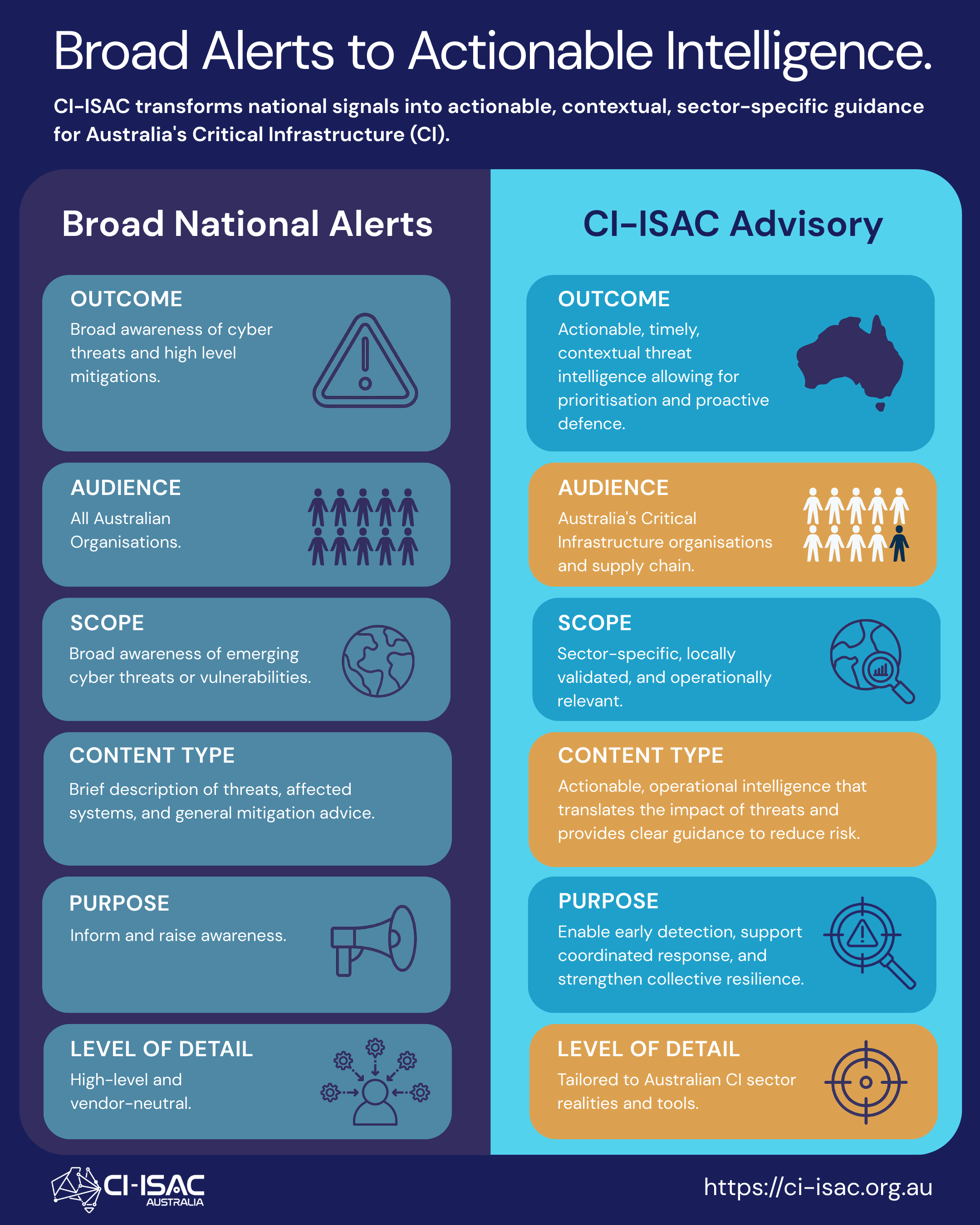
CI-ISAC Australia exists precisely for this, bringing together owners and operators across all 11 of Australia’s critical infrastructure sectors to share intelligence that has been validated and contextualised for Australian conditions, so that what one member observes, the broader network can act on.Access the intelligence network built for Australia’s critical infrastructure: Become a CI-ISAC member.




You must be logged in to post a comment.