Blog
Welcome to the CI-ISAC blog, your source for cutting-edge insights and thought leadership in the realm of cyber security. Here, we delve into the complexities of the digital landscape, offering expert analysis, innovative strategies, and valuable discussions aimed at fortifying our collective defences against cyber threats.
-

Australia’s health sector receives $6.4million cyber security boost with the creation of a new threat information-sharing network
CI-ISAC Australia has been selected as the recipient of an Australian Government $6.4 million grant to create a health-specific, information-sharing and analysis centre for Australia’s healthcare industry. Recent cyber-attacks on Australian healthcare organisations, including health funds and hospitals, have led the Australian Government to prioritise the healthsector, by identifying it as the first to receive
-

Data-driven insights & Accountability: Empowering Informed Decision-Making
In this 6th & final instalment of our series on strengthening Australia’s cyber threat intelligence sharing, we arrive at a crucial aspect often overlooked: how we analyse and operationalize the cyber threat information we share. Simply gathering and exchanging data, even within a sovereign framework, is insufficient. To effectively combat sophisticated cyber adversaries, we must
-

Forever Chasing the Ambulance: Why Reactive, Informal Cyber Threat Sharing Fails
In the previous instalments of this series, we’ve established the need for sovereign cybersecurity capabilities & highlighted the crucial difference between raw data and actionable intelligence. Now, we turn our attention to how we share cyber threat information, arguing that the method of sharing is just as critical as the information itself. Relying on unstructured,
-

Sovereign Cybersecurity: Safeguarding Australia’s Critical Infrastructure
Trust, control, and resilience: These principles are paramount in cybersecurity, especially when it comes to protecting national critical infrastructure. This fourth installment explores why sovereign capability is essential for secure information sharing and a stronger national cybersecurity posture. In today’s interconnected world, the battleground for modern warfare has expanded to include the digital realm. Critical
-

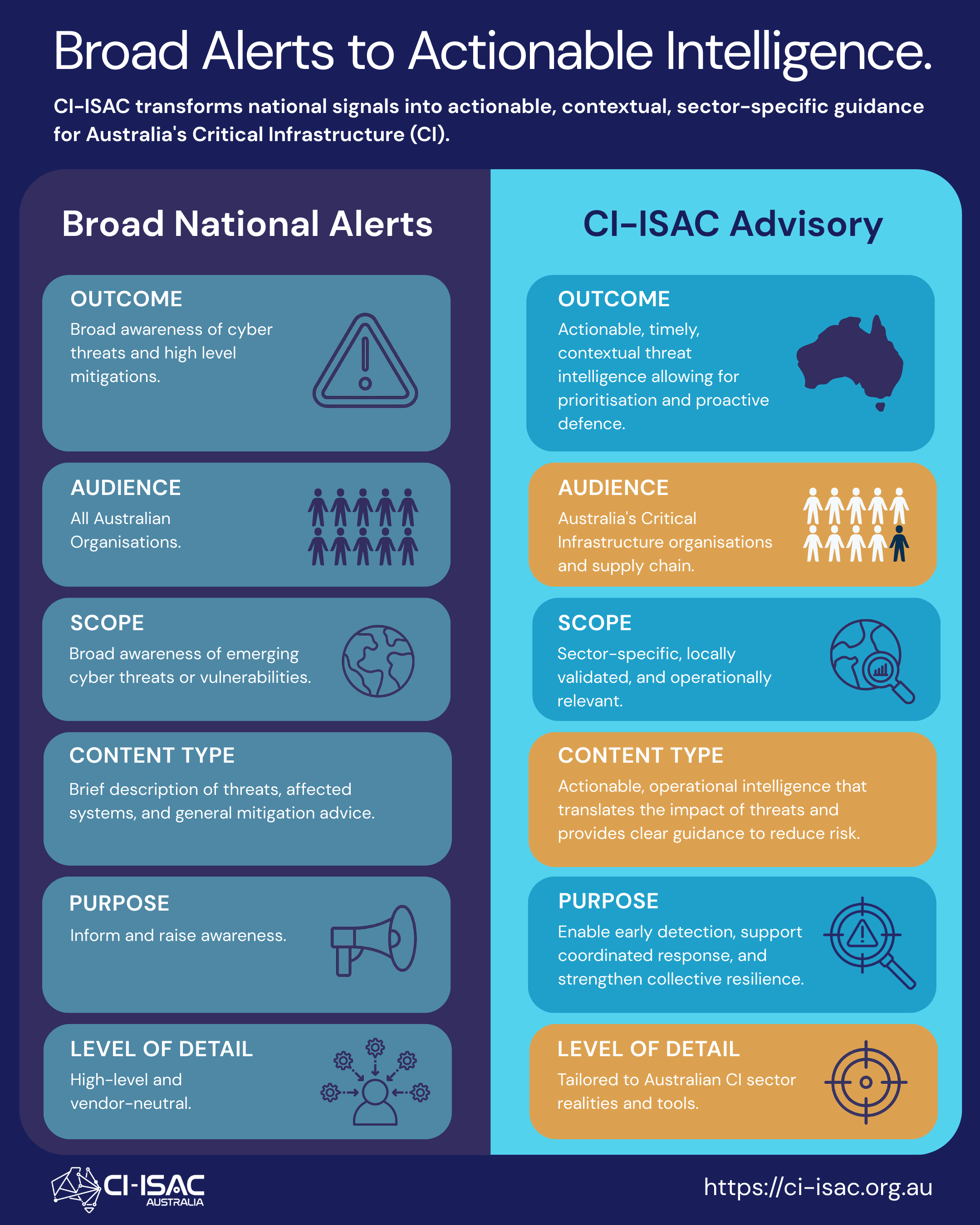
CTI Sharing – Information vs. Intelligence
Building on the previous two posts, this third instalment on CTI sharing explores why it is vital to draw a distinction between cyber information & cyber intelligence. We explain why understanding the difference between the two is crucial for effective cybersecurity management and decision-making. Australia’s cybersecurity hinges on bridging the gap between raw information and
-

The ‘Canary in a coal mine’ – A Business Cyber Risk Case Study
WhatsApp, Signal, iMessage: These everyday apps could be putting your organisation at significant risk, especially when it comes to your organisation sharing sensitive Cyber Threat Intelligence (CTI). This second installment delves into a recent US legal case that exposes the dangers of relying on informal communication channels & underscores the need for a more structured,
#strongertogether

CI-ISAC leverages membership fees to promote the collective uplift of all critical infrastructure defences, and as such members of all tiers gain access to the same core services and capabilities