Security Frameworks: A Foundation, Not a Finish Line
Security frameworks like ISO 27001, NIST, ASD’s Essential 8, and the AESCSF provide essential baseline standards for mitigating cyber threats. Compliance with these frameworks should be viewed as a minimum investment in establishing a broad set of controls to protect your organisation’s environment.
Beyond Frameworks: The Dynamic Landscape of Cyber Threats
Security frameworks and government regulations are inherently reactive, struggling to keep pace with the ever-evolving tactics of cyber attackers. These frameworks provide general guidelines, but they often fail to address the specific threats and vulnerabilities unique to your business and technical environment.
Cyber Threat Intelligence: Your Strategic Advantage for Proactive Risk Management
Cyber Threat Intelligence (CTI) offers a powerful solution for bridging this gap. CTI provides real-time insights into emerging threats, active campaigns targeting your industry, and new attack techniques that require proactive adjustments to your security controls.
Gaining a Competitive Edge Through CTI:
- Targeted Risk Assessment: CTI enables you to assess the relevance of specific threats to your organization’s security posture, helping you understand which vulnerabilities are most likely to be exploited.
- Prioritisation of Resources: By understanding the threats that pose the greatest risk, you can prioritize your resources and efforts on the areas that will deliver the most significant improvements in your cyber defences.
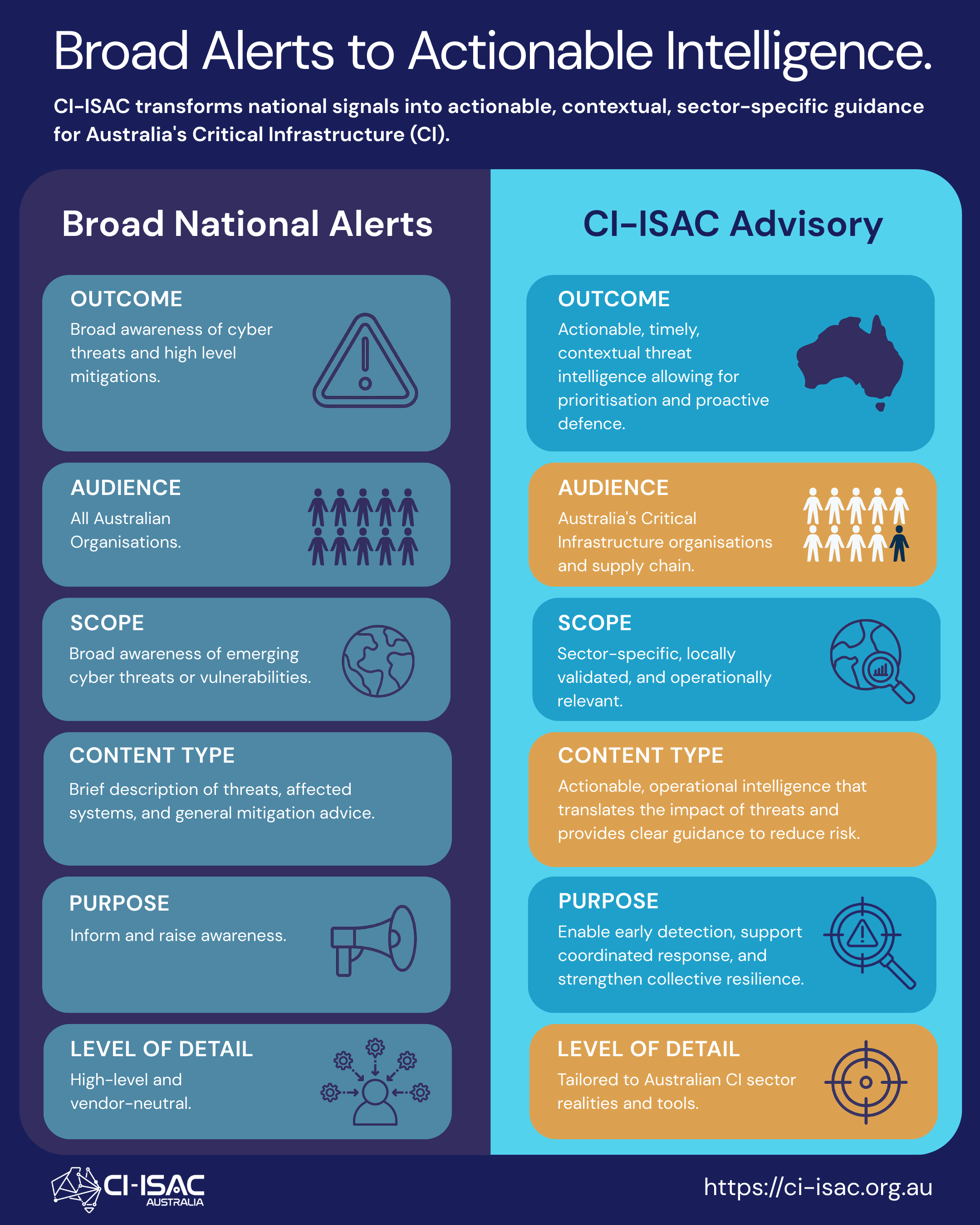
CI-ISAC provides members with timely and relevant cyber threat intelligence, including:
- Threat Advisories: Stay informed about the latest threats, vulnerabilities and attack techniques relevant to your sector.
- Contextual Analysis: Gain valuable insights into the implications of emerging threats and how they might impact your organization.
- Prioritisation Guidance: Clear recommendations on how to prioritise your security efforts based on the most critical risks.
Improve your Cybersecurity Posture with CI-ISAC:
By leveraging CI-ISAC’s threat intelligence, you can proactively identify and address relevant threats before they become significant risks, enhancing your organisation’s resilience and minimising the potential for costly breaches and data loss.