Introduction
Sharing groups can range from large, fully incorporated organisations (whether commercial or non-profit) that offer member interaction as part of their services, right down to smaller Signal / WhatsApp / Email-based groups where individuals share information on threats.
Information Sharing and Analysis Centers (ISACs) are non-profit organisations that provide a central resource for gathering information on cyber threats (in many cases to critical infrastructure) as well as allow two-way sharing of information between the private and the public sector about root causes, incidents and threats, as well as sharing experience, knowledge and analysis. (def: ENISA)
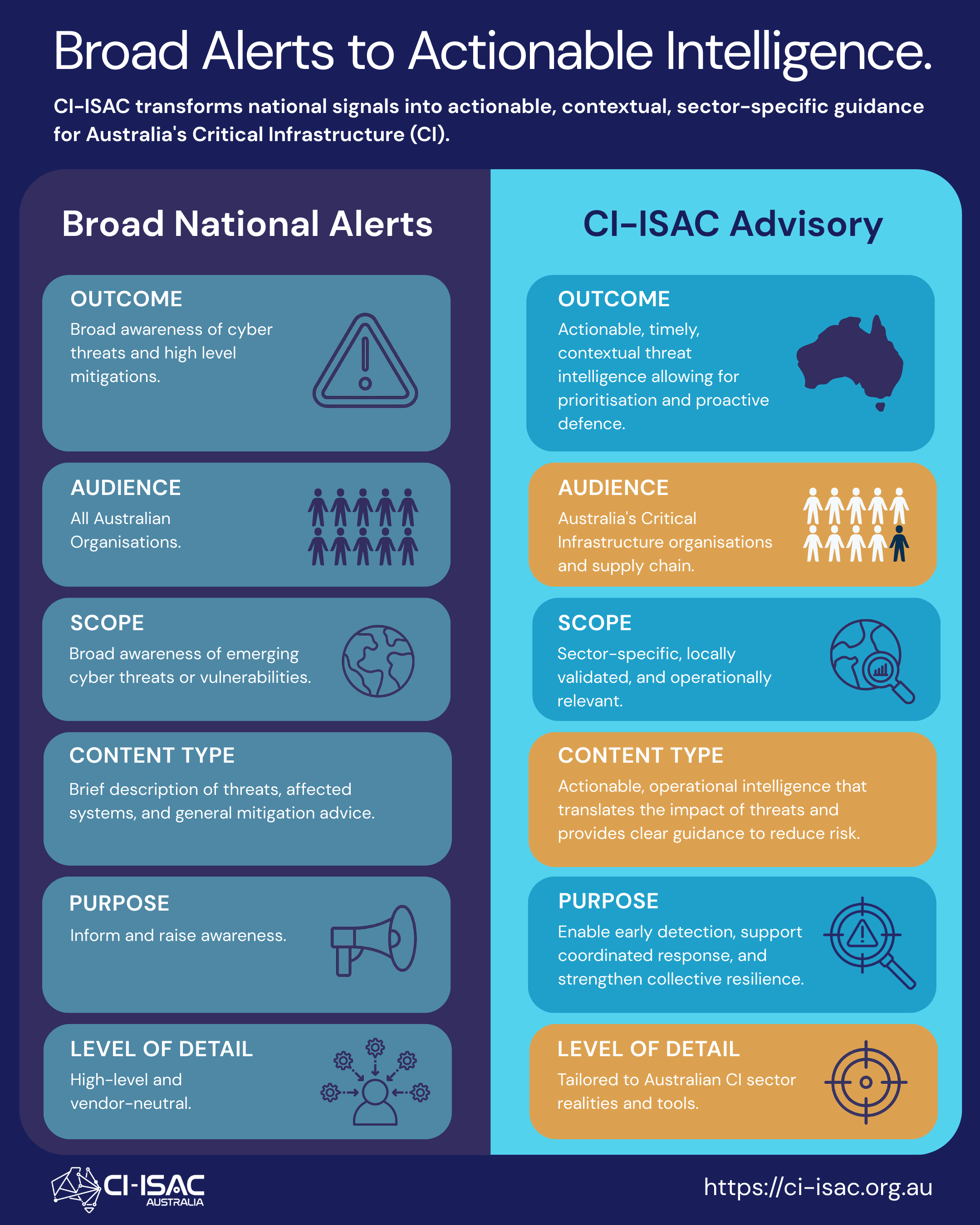
CI-ISAC extends the traditional ISAC model, which is less focussed on finished intelligence and more focussed on the dissemination of information, which still requires analysis by recipients. CI-ISAC takes a quality over quantity approach to reduce noise and issue threat advisories, which reduce the burden on individual recipients and fast-track their response efforts.
Benefits and Limitations
The following table outlines the benefits and limitations of unstructured (data, information) and structured (intelligence analysis) sharing arrangements.
Unstructured Sharing
Structured Sharing (CI-ISAC)
Benefits
- Accessibility: Low barrier to entry, anyone can easily join
- Cost: No / low cost to join
- Lightweight: Builds relationships among a specific group of members.
- Timely: Information can be shared quickly with the group
- Structure and Organisation: Defined goals, processes, and structure help ensure sharing is captured and benefits members.
- Information Quality: Shared Information is triaged, validated and analysed prior to being disseminated to members .
- Reduce Risk: Relevant intelligence is disseminated to members, reducing member overheads and enabling teams to focus on addressing relevant cyber risks.
- Outcome Focus: Analysis and insights are presented in a clear and concise manner, enabling decisions and action.
- Controlled Access: Confidentiality is protected through access restrictions and data encryption on sovereign platforms.
- Legal (Contractual) relationship between CI-ISAC and the member org provides board oversight and accountability
- Legal risk e.g. under SOCI and many other laws: wrongful dissemination of protected info has legal consequences
- Shared Information is anonymised: avoids legal risk
Limitations
- Structure: Typically loosely organised, informal and sharing is transactional and cannot be cross-referenced / used to identify trends.
- Limited Impact: Information likely to stay within the group and not benefit a wider audience.
- Inaccurate or Biased Information: No verification or quality control mechanisms around shared information.
- Information Overload: Difficult to manage the flow of information and distinguish valuable insights.
- Confidentiality Issues: No confidentiality protections, lack of data handling hinders ability to share more widely.
- Cost: Requires dedicated staff, technology, and resources, resulting in a financial cost for members (based on entity size).
- Accessibility: Formal membership requires effort from members to onboard and prioritise sharing via sovereign platforms.
- Uptake: Cost and accessibility makes acquiring additional members more time consuming, with the full ‘network effects’ of sharing being driven by the number of active participants.
Structured sharing filters noise to drive outcomes

The fundamental purpose of these groups, regardless of their structure, is to facilitate information sharing for the benefit of their members. For the purposes of this comparison, any group or forum that does not validate and capture outputs using a structured format to conduct further analysis is going to be limited in the outcomes it can deliver to participants.
For additional information on the perils of informal sharing, read our blog post here.




You must be logged in to post a comment.