Australia’s evolution of its cyber security strategy over the past decade has been accompanied by a growing recognition of the need to uplift the security and resilience of our critical infrastructure. This acknowledges the fact that Australia’s Critical Infrastructure sector underpins our economy and society; its security and resilience is central to sustaining the Australian way of life.
Threats to critical infrastructure continue to grow. Cyber theft and attacks on critical infrastructure coupled with the perpetual threats of natural disasters such as floods and fires, and nation state attacks, create a complicated threat environment for critical infrastructure owners/operators and Government alike. Critical Infrastructure Protection is now identified as a material area of national security risk.
As Australia’s critical infrastructure becomes increasingly interconnected and interdependent in its operations, there is an appreciation that this connectivity creates vulnerabilities unless proper safeguards are put in place.
Addressing this material area of risk and introducing safeguards demands a better shared understanding of the threats Australia faces and how they can be overcome, to bolster the security and resilience of the nation’s critical infrastructure.
But what is Critical Infrastructure? The Security of Critical Infrastructure Act 2018 (SOCI Act) describes Critical Infrastructure as:
‘those physical facilities, supply chains, information technologies and communication networks which, if destroyed, degraded or rendered unavailable for an extended period, would significantly impact the social or economic wellbeing of the nation or affect Australia’s ability to conduct national defence and ensure national security.’
The Australia’s Security Legislation Amendment (Critical Infrastructure Protection) Act 2022 amendments to the SOCI Act 2018 feature an expanded list of what constitutes critical infrastructure, as well as new regulations and obligations which has significantly raised the cyber-security standard for many organisations.
Cyber protection is a continuous process as threats continue to advance and multiply, and new skillsets and policies need to be developed to respond. There are currently 11 industries covered by the SOCI Act, but as our understanding of cyber and critical infrastructure grows, particularly of critical infrastructure’s dependencies with other sectors of the economy, this number is likely to grow. That means all industries must start to take control of their cyber defences, including protecting more than their IT assets. For example, paying closer attention to insider threats. Compliance to the SOCI Act amendments shouldn’t be seen as a cost burden to business, but as an opportunity for a holistic examination of risk. Critical Infrastructure risk management is an enduring function that must be part of business as usual.
The Minister for Home Affairs has exercised her power to declare a significant number of Systems of National Significance, which require extended obligations, and has introduced a Mandatory Cyber Incident Regime. However, legislation and regulatory approaches will always lag threats; therefore, there is a pressing need for collaboration across the critical infrastructure ecosystem, leveraging individual strengths to improve the collective posture through innovative approaches within given constraints around the need to continue operations, deal with legacy assets, and costs in uplifting defences.
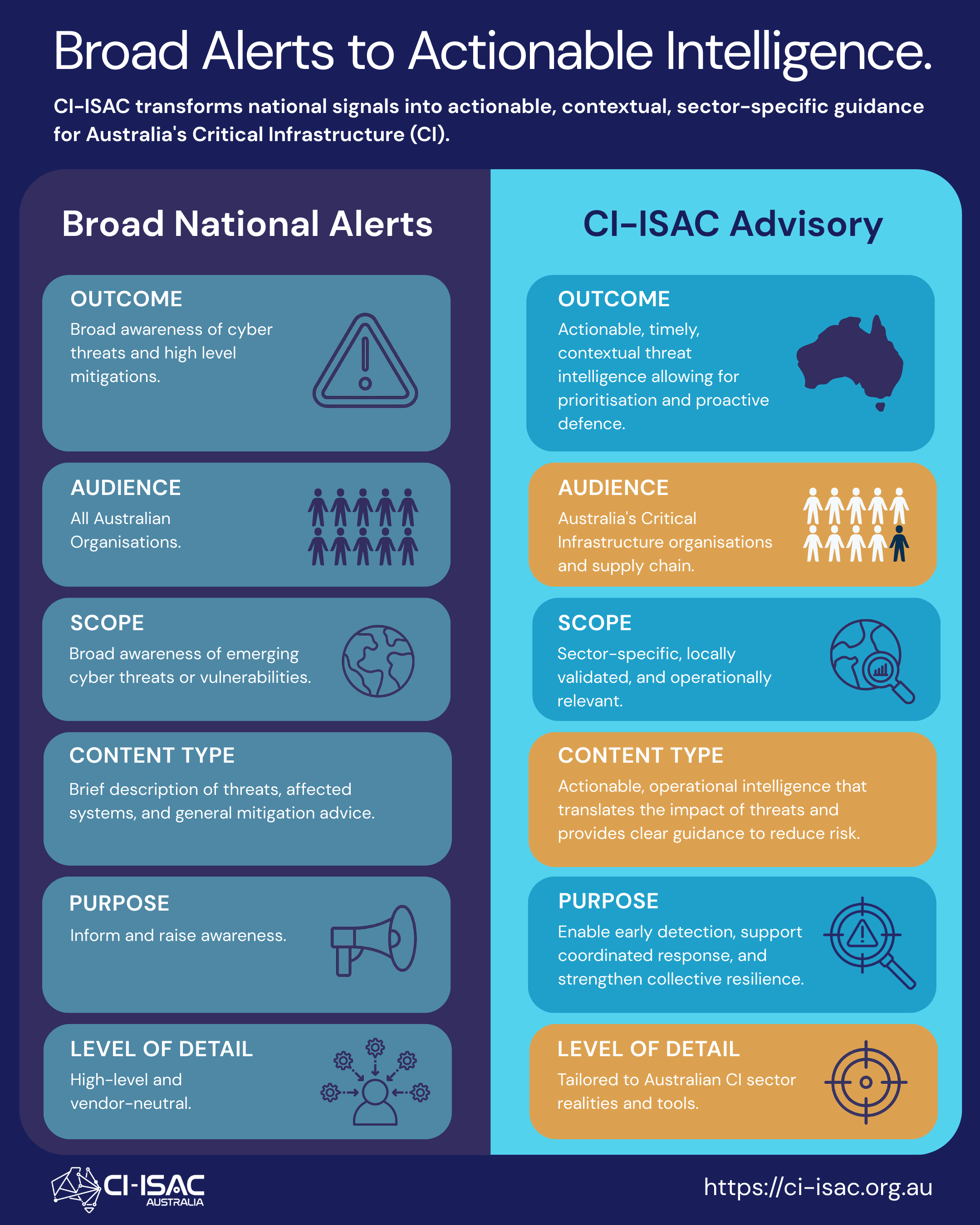
A key innovative approach would be to institute a national cross-sectoral cyber-threat intelligence (CTI) sharing capability for critical infrastructure. Threat intelligence must be timely, relevant, and contextualised so that it can be used by business, technology, and security professionals. The CTI program must collect, process, and analyse the right data – not necessarily the most data. It must enrich alerts, help organisations create a threat-informed defence, and align cyber risks with business initiatives. It must also continuously adapt against new threats and adversaries. Priority Intelligence Requirements must be aligned with business and mission objectives.
The best time to do this was in conjunction with the 2020 cyber security strategy. That didn’t happen. The next best time is now.
Originally published on LinkedIn, 1st November 2023